Archive
Libya Crackdown on Protests Kills 24: Rights Group
CAIRO – Libyan security forces killed at least 24 people in a violent crackdown on anti-regime demonstrations during a “Day of Anger” against strongman Moamer Kadhafi, Human Rights Watch said Friday. The New York-based rights group, citing witnesses, said 24 protesters were killed and scores injured during Thursday’s assaults on protests in two Libyan cities. The New York-based rights group, citing witnesses, said 24 protesters were killed and scores injured during Thursday’s assaults on protests in two Libyan cities.
The New York-based rights group, citing witnesses, said 24 protesters were killed and scores injured during Thursday’s assaults on protests in two Libyan cities. The New York-based rights group, citing witnesses, said 24 protesters were killed and scores injured during Thursday’s assaults on protests in two Libyan cities.
“The authorities should cease the use of lethal force unless absolutely necessary to protect lives and open an independent investigation into the lethal shootings,” HRW said in a statement.
The regime of Kadhafi, who has been in power since 1969, vied to counter the swelling opposition movement with its own pro-government rallies in the capital Tripoli and other cities.
But the unrest has deepened as the opposition mobilises via Facebook and mobile phone messages, emulating protest movements across North Africa and the Middle East that have already brought down the regimes in Egypt and Tunisia.
Geneva-based Human Rights Solidarity, citing witnesses, meanwhile said rooftop snipers in Read more…
The Fed is Wrong About Commodity Prices
Author: David Weinstein
I imagine he has to say it, but Bernanke is wrong when he says US monetary policy has nothing to do with international commodity prices. At the height of the Egyptian crisis, which was partly driven by rising food prices, Bernanke couldn’t say, “Oh yea, US policy economic policy is part of the problem in Egypt.” This attitude, however, is both prevalent and respected, and it’s largely wrong.
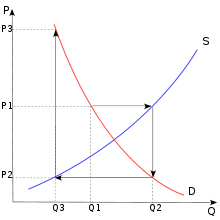
First of all, commodities as a group are not commoditized – they are not all the same. For instance, the amount of gold in the world is largely fixed relative to annual gold production. Along with its historical position as a store a value, Gold’s consistent volume about ground is a primary reason for its currency-like quality; i.e. almost entirely driven by overall liquidity. Corn production, on the other hand can vary greatly from year to year given the amount of land devoted to it and the weather. Oil is somewhere in the middle because production can vary, but the worlds known reserves are relatively fixed. The resulting differences in price volatility have been studied ad nauseam and are most simply articulated by the so-called ‘cob-web model’ (see chart below).
Very simply put: Read more…
The Internet Kill Switch
 This past week was a perfect example of how the “Internet kill switch” is rapidly becoming one of the favorite new tools of tyrannical governments all over the globe. Once upon a time, the Internet was a bastion of liberty and freedom, but now nation after nation is cracking down on it. In fact, legislation has been introduced once again in Congress that would give the president of the United States an “Internet kill switch” that he would be able to use in the event of war or emergency. Of course there would be a whole lot of wiggle room in determining what actually constitutes a true “emergency”. The members of Congress that are pushing this “Internet kill switch” bill want the U.S. to become more like China in this regard. In China, the Internet is highly controlled, highly regulated and highly censored. In fact, China has shut down the Internet in entire regions when they have felt it necessary. So what Egypt did in shutting down the Internet this past week is not unprecedented – but it was quite shocking.
This past week was a perfect example of how the “Internet kill switch” is rapidly becoming one of the favorite new tools of tyrannical governments all over the globe. Once upon a time, the Internet was a bastion of liberty and freedom, but now nation after nation is cracking down on it. In fact, legislation has been introduced once again in Congress that would give the president of the United States an “Internet kill switch” that he would be able to use in the event of war or emergency. Of course there would be a whole lot of wiggle room in determining what actually constitutes a true “emergency”. The members of Congress that are pushing this “Internet kill switch” bill want the U.S. to become more like China in this regard. In China, the Internet is highly controlled, highly regulated and highly censored. In fact, China has shut down the Internet in entire regions when they have felt it necessary. So what Egypt did in shutting down the Internet this past week is not unprecedented – but it was quite shocking.
Google Comes Under Fire for ‘Secret’ Relationship with NSA
 Consumer Watchdog, an advocacy group largely focused in recent years on Google’s privacy practices, has called on a congressional investigation into the Internet giant’s “cozy” relationship with U.S. President Barack Obama’s administration.
Consumer Watchdog, an advocacy group largely focused in recent years on Google’s privacy practices, has called on a congressional investigation into the Internet giant’s “cozy” relationship with U.S. President Barack Obama’s administration.
In a letter sent Monday, Consumer Watchdog asked Representative Darrell Issa, the new chairman of the House Oversight and Government Reform Committee, to investigate the relationship between Google and several government agencies.
The group asked Issa to investigate contracts at several U.S. agencies for Google technology and services, the “secretive” relationship between Google and the U.S. National Security Agency, and the company’s use of a U.S. National Aeronautics and Space Administration airfield in California.
Federal agencies have also taken “insufficient” action in response to revelations last year that Google Street View cars were collecting data from open Wi-Fi connections they passed, Consumer Watchdog said in the letter.
“We believe Google has inappropriately benefited from close ties to the administration,” the letter said. “Google is most consumers’ gateway to the Internet. Nonetheless, it should not get special treatment and access because of a special relationship with the administration.” Read more…
How Egypt shut down the internet
Virtually all internet access in Egypt is cut off today as the government battles to contain the street protests that threaten to topple President Hosni Mubarak.

Organisations that track global internet access detected a collapse in traffic in to and out of Egypt at around 10.30GMT on Thursday night.
The shut down involved the withdrawal of more than 3,500 Border Gateway Protocol (BGP) routes by Egyptian ISPs, according to Renesys, a networking firm. Only one ISP out of 10, Noor Data Networks, appeared largely unaffected. It connects to the outside world via an undersea cable operated by Telecom Italia.
According to BGPMon, another networking firm, 88 per cent of Egyptian internet access was successfully shut down, however.
Renesys speculated that the apparent anomaly of Noor Data Networks may be a result of the fact it provides services to the Egyptian stock exchange. Read more…
Four Cyber Threats for 2011
Internet Superweapons to Facebook Crimes, Security Experts Predict New Web Attacks
 In late 2010, a new kind of computer worm attacked an Iranian nuclear facility and so altered the course of cyber warfare that the U.S. Senate Committee on Homeland Security and Governmental Affairs marked the attack as the beginning of a new era: The Age of Stuxnet.
In late 2010, a new kind of computer worm attacked an Iranian nuclear facility and so altered the course of cyber warfare that the U.S. Senate Committee on Homeland Security and Governmental Affairs marked the attack as the beginning of a new era: The Age of Stuxnet.
And while the Stuxnet worm may be the most identifiable, ominous new threat to cyber security as the new year begins, security experts have predicted 2011 will also be a year of dynamic shifts in online threats in other areas, including social media and political “hacktivism.”
Here are the top four security concerns that cyber experts see coming over the digital horizon:
Cyber War’s Newest Superweapon: Stuxnet and Copycats
Stuxnet was first discovered in July 2010 by a security firm in Belarus, but didn’t make global headlines until months later when Iranian state media announced the Middle East nation had been the target of a coordinated attack.
The worm was “the first of its kind, written to specifically target mission-critical control systems running a specific combination of software and hardware,” a Department of Homeland Security official told ABC News.
But experts said the worm is not limited to any single type of target and can be altered to attack several key components of any nation’s infrastructure, from electricity grids to oil rigs.
“The idea that a piece of malicious code can target physical systems and create real-world impacts is something that’s been speculated in the industry for quite some time and certainly was largely understood to be possible. Stuxnet was the first widespread implementation of that kind of attack,” Ben Greenbaum, senior research manager for cyber security firm Symantec, told ABC News.
Symantec’s number one prediction for 2011 was increased cyber attacks on critical infrastructures just like the nuclear facility in Iran, and Stuxnet is only the beginning. Read more…


![[Most Recent Quotes from www.kitco.com]](https://i0.wp.com/www.kitconet.com/charts/metals/gold/t24_au_en_usoz_2.gif)
![[Most Recent Quotes from www.kitco.com]](https://i0.wp.com/www.kitconet.com/charts/metals/silver/t24_ag_en_usoz_2.gif)

You must be logged in to post a comment.